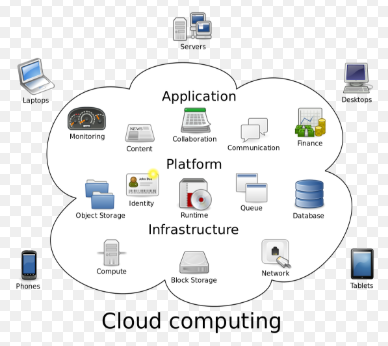
Cloud computing is the on-demand availability of computer system resources, especially data storage and computing power, without direct active management by the user.
Service Models
- IAAS Infrastructure as a Service: cloud provider hosts the infrastructure components traditionally present in an on-premises data center, including servers, storage and networking hardware, as well as the virtualization or hypervisor layer
- PAAS Platform as a Service: Geared toward application development and deployment. Platforms offer compute and storage infrastructure, as well as software development and deployment tools such as text editing, version management, compilation and build testing services (regressions)
- SAAS Software as a Service: software distribution model in which a third- party provider hosts applications and makes them available to customers over the Internet.
Cloud Characteristics
- On Demand / Self Service: characteristic of cloud computing that allows consumers to unilaterally provision computing capabilities without human interaction from the service provider where virtualized assets not part of your permanent IT infrastructure
- Measured Services: characteristic of cloud computing that allows systems to automatically control and optimize resource utilization by leveraging a metering capability at some level of abstraction appropriate to the type of service
- Multi- Tenancy: Each tenant in a cloud is much like the tenant of an apartment in a building. You have your own tenancy, which has resources you can build, change, and use as you see fit – within the limits, quotas, and rules set by the cloud owner. Additionally, no one else can touch anything in your tenancy except you and the cloud owner, and the owner is very limited in what they can do within your “apartment.” You can also freely choose to share some or all of what you’re doing with other tenants in the same cloud, or the greater internet in general as you see fit. Rather than being done with physical keys, segregation of this nature in the cloud is done by isolating traffic to VLAN’s and subnets, as well as by requiring digital keys and key-pairs to gain access.
- Resource Pooling: characteristic of cloud computing that provides computing resources are pooled to serve multiple Consumers using a multi- tenant model, with different physical and virtual resources dynamically assigned and reassigned based on consumer demand
- Horizontal Scaling
- Rapid Elasticity: characteristic of cloud computing that gives you the ability to expand and reduce resources according to your specific service requirements
- Broad Network Access
Shared Responsibility Model: concept that AWS and the customer share responsibilities for security and compliance of Amazon Web Services. This allows AWS to support the customer by taking on the burden of operations control associated with the physical infrastructure so the customer can focus on securing and producing within the context of software (logical).
Cloud Actors
- Cloud Provider: A cloud provider is a person, or an organization; it is the entity responsible for making a service available to interested parties. Cloud Provider acquires and manages the computing infrastructure required for providing the services, runs the cloud software that provides the services, and makes arrangement to deliver the cloud services to the Cloud Consumers through network access.
- Cloud Consumer: The cloud consumer is the principal stakeholder for the cloud computing service. A cloud consumer represents a person or organization that maintains a business relationship with, and uses the service from a cloud provider.
- Cloud Broker: A cloud broker is an entity that manages the use, performance and delivery of cloud services and negotiates relationships between cloud providers and cloud consumers. In general, a cloud broker can provide services in three categories:
- Service Intermediation: A cloud broker enhances a given service by improving some specific capability and providing value-added services to cloud consumers. The improvement can be managing access to cloud services, identity management, performance reporting, enhanced security, etc.
- Service Aggregation: A cloud broker combines and integrates multiple services into one or more new services. The broker provides data integration and ensures the secure data movement between the cloud consumer and multiple cloud providers.
- Service Arbitrage: Service arbitrage is like service aggregation except that the services being aggregated are not fixed. Service arbitrage means a broker has the flexibility to choose services
from multiple agencies. The cloud broker, for example, can use a credit-scoring service to measure and select an agency with the best score.
- Cloud Auditor: A cloud auditor is a party that can perform an independent examination of cloud service controls with the intent to express an opinion thereon. Audits are performed to verify conformance to standards through review of objective evidence. A cloud auditor can evaluate the services provided by a cloud provider in terms of security controls, privacy impact, performance, etc.
- Cloud Carrier: The intermediary that provides connectivity and transport of Cloud Services between Cloud Providers and Cloud Consumers. – Provides access to cloud consumers through network, telecommunication and other access devices.
Deployment Models
- Public Cloud: A public cloud is one based on the standard cloud computing model, in which a service provider makes resources, such as virtual machines (VMs), applications or storage, available to the general public over the internet. Public cloud services may be free or offered on a pay-per-usage model. Ie AWS, GOOGLE, AZURE
- Private Cloud: The private cloud is defined as computing services offered either over the Internet or a private internal network and only to select users instead of the general public. Typically this is on hosted hardware. Ie VMWARE
- Hybrid Cloud: cloud computing environment that uses a mix of on- premises, private cloud and third-party, public cloud services with orchestration between the two platforms.
- Community Cloud: A community cloud in computing is a collaborative effort in which infrastructure is shared between several organizations from a specific community with common concerns (security, compliance, jurisdiction, etc.), whether managed internally or by a third-party and hosted internally or externally.
Identity Access Control Service Access Control Resource Access Control
Federation
Orchestration
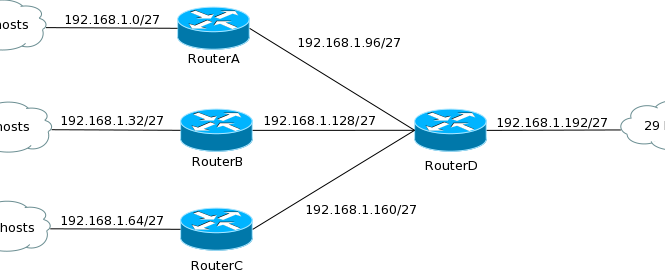
Virtual Private Cloud (VPC): Core networking component in AWS Cloud provides isolated container for AWS services resembling traditional networks. Fully realized in software with Subnets Routes Firewalls Implementing Router & Switch Functions to transport huge amounts of packets across AWS zones and IN/OUT of VPC. VPC also supports extended network services Elastic IP Addresses, Elastic Network Interface, AWS Endpoint, Elastic Load Balancer, DNS Services (Route53), Internet Gateways VPC Best Practices:
Choose highest CIDR block Unique IP Address to support AWS services Leave default VPC alone Including main route table Design for region expansion Tier your subnets Design subnets according to application stack (.ie Application tier, Business tier, Database tier) Spread across multiple availability zones for fault Tolerance Keep subnets balanced with appropriate routing tables Keep most resources in the private subnet (insulation) Use elastic load balancer in front of all outward exposed services Use different VPCs for different use cases (no one catch all VPC) Use Security Groups over NACLs IAM your VPC (least Privilege) Leverage VPC peering Use elastic IP instead of public IP
Amazon Machine Image Simple Storage Service Elastic Block Storage Elastic Compute Cloud Elastic IP: Public IPv4 static address associated with any one instance or network interface When you need an IP address to persist you need to use elastic IP addresses as public addresses are recycled when the instance Is shutdown. Elastic IP is portable and can be moved to another running instances Elastic Load Balancing: Provides high availability insulation layer to AWS resources by allowing private subnet to be exposed through secure channels
Identity and Access Management
Groups Users Roles Policies
Secure Server Best Practices Least Access Least Privilege Configuration Management Change Management Audit Logs Network Access API Access Data Encryption
AWS Secure Communication Model (data in flight)
Console CLI API
Data at Rest: state of data while it persists in a storage medium
Encryption fundamentals Symmetric Encryption: Same key for encryption and decryption Not viable where sender and receiver never meet (no way to get key there) Asymmetric Encryption: Different keys for encryption Public/Private Public encrypts Private Decrypts
Encryption: Conversion of plaintext into ciphertext where remnants of language are removed (semantic patterns) Decryption: Conversion from ciphertext back to plain text Two-part process: Encryption Key: Unique value of variable length (longer is better) Algorithm (Cipher): Function that takes as input plain text string and key and returns cipher text
AWS does not use asymmetric encryption (performance) AWS Encryption Envelope 1. AWS Service generates data key when user requests data to be encrypted 2. This key is used to encrypt data along with the encryption algorithm 3. Once data is encrypted, key is encrypted as well 4. Both key and data are stored in AWS storage service Process requires independent master key (managed separately from data and data key) to encrypt data key Process is reversed for decryption
AWS KMS Key Management Service Asymmetric Key Service Fully Managed Centralized key Management Fully integrated with the AWS Service Suite Secure and Compliant SOC1, SOC2, SOC3 ISO-9001 PCI-DSS Level1